A new ransomware-as-a-service (RaaS) operation, GLOBAL GROUP, has emerged with notable AI-driven negotiation capabilities, targeting various sectors including healthcare, automotive, and industrial. Since its inception in June 2025, the operation has reportedly claimed 17 victims worldwide, showcasing an efficient operational model that leverages automated systems and strategic partnerships.
"GLOBAL GROUP launched on June 2, 2025, when the threat actor known as '$$$' introduced the operation on the Ramp4u cybercriminal forum," stated a report by cybersecurity researchers. The group quickly established itself, with a dedicated leak site that became operational shortly after its launch, revealing victim information via a Tor address.
"GLOBAL GROUP launched on June 2, 2025, when the threat actor known as '$$$' introduced the operation on the Ramp4u cybercriminal forum,"

In just five days, the group's leak site listed nine victims, underscoring their aggressive approach. By mid-July 2025, this number had surged to 17 confirmed targets located in countries such as the United States, the United Kingdom, Australia, and Brazil. Analysts from EclecticIQ believe that GLOBAL GROUP is most likely a rebranding of the previous Black Lock RaaS operation. The evidence supporting this assertion includes shared infrastructural ties, notably hosted by a Russian provider.
"Technical evidence supports this connection," noted analysts, highlighting the operational oversight that exposed crucial infrastructure details. Furthermore, a leak from the group's API endpoint included metadata revealing its hosting environment.
"Technical evidence supports this connection,"

Phishing has taken a new turn with GLOBAL GROUP. Their malware analysis indicates the operation uses a tailored variant of the Mamona ransomware. This version has been adapted to enhance functionality and deploy a sophisticated encryption method called ChaCha20-Poly1305. "The current variant, compiled in Golang, is versatile, enabling deployment across Windows, Linux, and macOS platforms," explained a malware researcher.
"The current variant, compiled in Golang, is versatile, enabling deployment across Windows, Linux, and macOS platforms,"
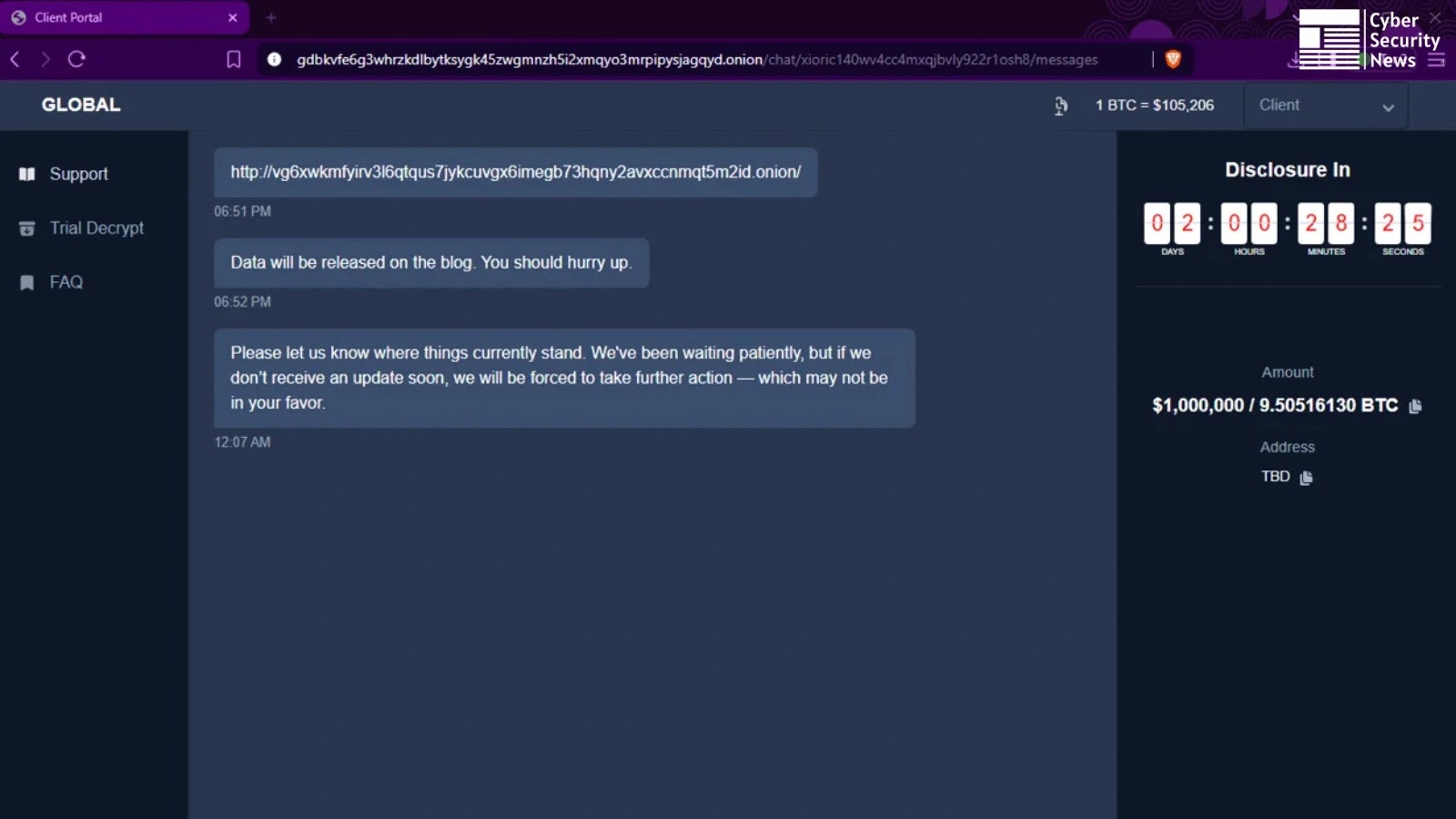
One of the standout features of GLOBAL GROUP is its AI-powered negotiation system. This innovation is designed to assist non-English speaking affiliates in effectively communicating with victims. "This automated system increases psychological pressure during ransom negotiations and facilitates seven-figure payment demands," explained an industry expert. It's reported that some demands have reached as high as $1 million USD, demonstrating a bold new standard in ransom requests.
"This automated system increases psychological pressure during ransom negotiations and facilitates seven-figure payment demands,"
Moreover, GLOBAL GROUP has developed partnerships with Initial Access Brokers, which accelerates their operational deployment. "These partnerships combined with brute-force tools, especially targeting VPNs and Outlook systems, have allowed GLOBAL GROUP to bypass traditional endpoint detection and response (EDR) measures," added security experts.
"These partnerships combined with brute-force tools, especially targeting VPNs and Outlook systems, have allowed GLOBAL GROUP to bypass traditional endpoint detection and response (EDR) measures,"
This operation also incorporates a mobile-friendly affiliate panel that appeals to new recruits by offering an enticing revenue-sharing model. “The affiliate structure, featuring an 85% revenue-sharing model, is designed to attract a wider pool of operatives, enhancing their operational reach,” stated an analyst closely following the RaaS landscape.
As the cryptocurrency boom continues, criminals like those behind GLOBAL GROUP are adapting to leverage these market conditions for ransom payments. The inclusion of AI in negotiations represents a significant evolution in ransomware tactics, signaling potential challenges for law enforcement and cybersecurity professionals alike.
Moving forward, the cybersecurity community will need to remain vigilant against the evolving threats posed by RaaS operations. With capabilities like AI-generated negotiations, the negotiation landscape is undergoing a radical transformation, compelling stakeholders to rethink their strategies in combating this pervasive threat.