In a significant cybersecurity event, Denmark's critical infrastructure was subjected to the largest recorded cyber attack in the nation’s history, according to Denmark’s SektorCERT, the Computer Security Incident Response Team for critical infrastructure.
The attack unfolded in two waves, with the first commencing on May 11, followed by a second wave on May 22. "SektorCERT became aware of the attacks on May 22," the report noted, detailing the series of incidents that prompted concern across various sectors.
"SektorCERT became aware of the attacks on May 22,"
The scale of the attack was alarming, as 22 companies involved in the energy infrastructure were impacted. Of these, 11 companies faced immediate breaches due to attackers exploiting zero-day vulnerabilities in Zyxel firewalls, which are widely used among critical infrastructure operators in Denmark.

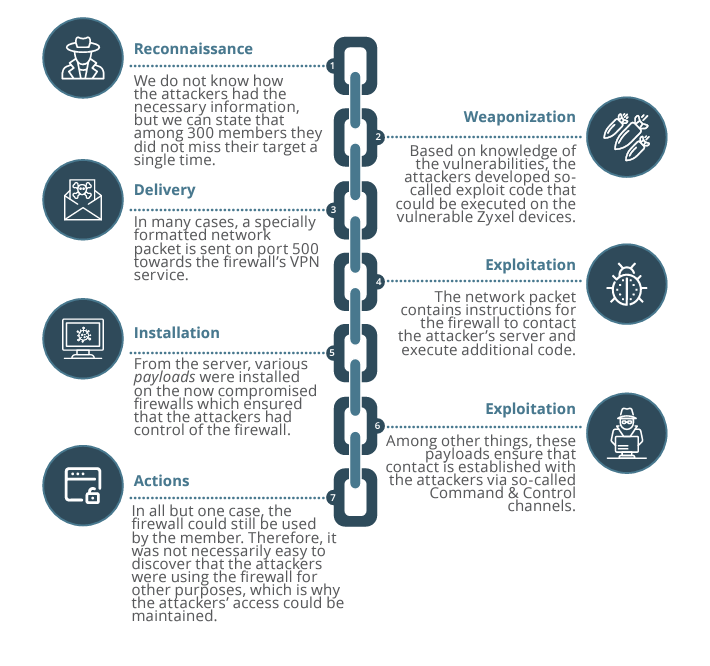
On April 25, 2023, Zyxel had revealed a critical vulnerability (CVE-2023-28771) with a CVSS score of 9.8. The flaw pertained to improper error message handling in several firewall firmware versions, allowing remote, unauthenticated attackers to execute OS commands by sending specially crafted packets. "Improper error message handling in some firewall versions could allow an unauthenticated attacker to execute some OS commands remotely by sending crafted packets to an affected device," read the advisory issued by Zyxel.
"Improper error message handling in some firewall versions could allow an unauthenticated attacker to execute some OS commands remotely by sending crafted packets to an affected device,"
Race Results
SektorCERT elaborated on the nature of the attack: "The vulnerability itself was exploited by sending a single specially crafted data packet to port 500 over the protocol UDP towards a vulnerable Zyxel device. The result was that the attacker could execute commands with root privileges directly on the device without authentication."
The revelation that attackers gained control of firewalls at multiple companies raised questions about the level of planning and reconnaissance that was involved. "The attackers had detailed information about the targets, likely obtained through a previously undetected reconnaissance activity," SektorCERT concluded.
"The attackers had detailed information about the targets, likely obtained through a previously undetected reconnaissance activity,"
The incident demonstrated a level of coordination that suggests a well-organized effort. "To this day, there is no clear explanation of how the attackers had the necessary information, but we can state that among the 300 members, they did not miss a single shot," the experts stated in their report. The ability to mount simultaneous attacks minimized the chance of information sharing among affected organizations, which is typically crucial in identifying and mitigating threats.
"To this day, there is no clear explanation of how the attackers had the necessary information, but we can state that among the 300 members, they did not miss a single shot,"

The sophistication of the attacks led analysts to propose that advanced persistent threat (APT) groups were involved. "Whether Sandworm was involved in the attack cannot be said with certainty. Individual indicators of this have been observed, but we have no opportunity to neither confirm nor deny it," the report highlighted. Sandworm, thought to have connections to Russia, is one potential contender within the spectrum of possible attackers.
The findings from the SektorCERT report included indicators of compromise (IOCs) observed during the attacks. However, experts cautioned about the difficulty in attributing such cyber attacks to specific groups or nations. "Cyber attacks are notoriously difficult to attribute to a specific attacker, and often it is small, almost insignificant errors from the attacker that can indicate who the attacker may be," they noted.
"Cyber attacks are notoriously difficult to attribute to a specific attacker, and often it is small, almost insignificant errors from the attacker that can indicate who the attacker may be,"
In conclusion, the incident concerning Denmark's critical infrastructure underscores the vulnerabilities that exist within large-scale systems. It serves to remind stakeholders of the evolving threat landscape and the critical need for robust security protocols and continuous monitoring of infrastructure networks to defend against increasingly sophisticated cyber threats. The implications of this attack will likely resonate for some time as further investigations proceed, and best practices are refined in response to this unprecedented event.