A new threat has emerged in the cybersecurity landscape: Ymir ransomware. Recently identified by Kaspersky researchers, Ymir is deployed shortly after systems are infiltrated using PowerShell commands and is characterized by its stealthy tactics and advanced evasion techniques.
"A link between malware stealer botnets acting as access brokers and the ransomware execution is evident," reads the Kaspersky report. This observation underscores the growing complexity of ransomware deployment methods. In particular, Ymir uses sophisticated methods to execute tasks in memory, leveraging functions such as `malloc`, `memmove`, and `memcmp` to obscure its activities from standard detection measures.
"A link between malware stealer botnets acting as access brokers and the ransomware execution is evident,"
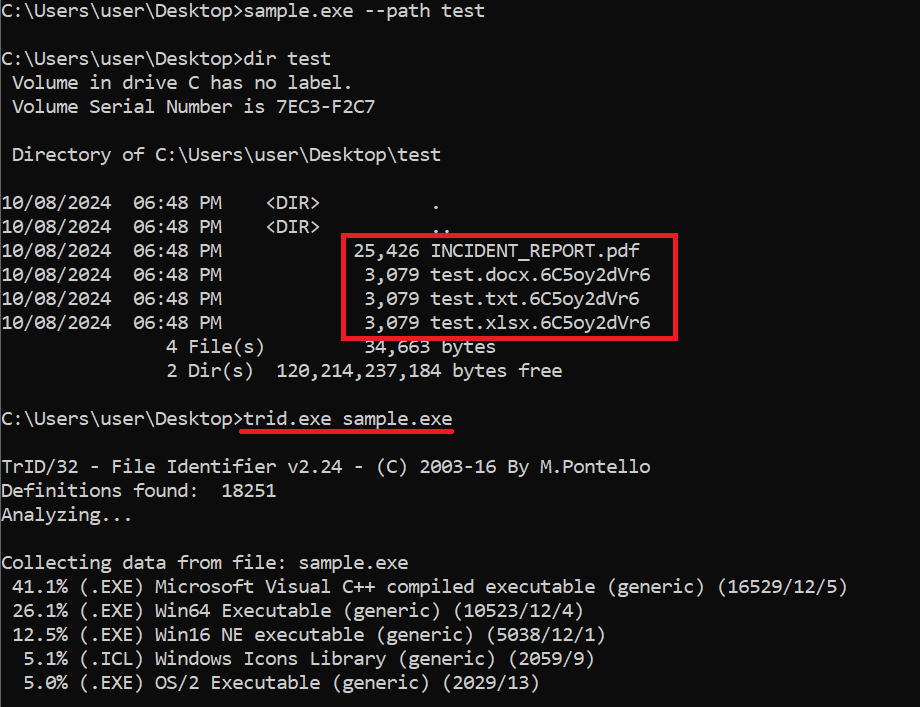
The ransomware utilizes the ChaCha20 stream cipher to encrypt compromised files, subsequently appending a unique extension, '.6C5oy2dVr6', to the affected file names. This unique naming convention complicates recovery efforts for victims.

Notably, Ymir's first observed deployment in a Colombian incident came just two days after threat actors executed RustyStealer, a malware variant that operates by harvesting sensitive information and controlling compromised systems. RustyStealer, masquerading as an innocuous executable named AudioDriver2.0.exe, successfully infiltrated multiple systems, including domain controllers that possess privileged access.
Career Journey
"The group behind this threat has not presented a dedicated leak site or any additional information yet, but we will continue monitoring their activity," the report states, indicating that the Ymir group is still in its early operational phase. This shift signals a potential departure from traditional Ransomware-as-a-Service (RaaS) models, as outlined by researchers.
"The group behind this threat has not presented a dedicated leak site or any additional information yet, but we will continue monitoring their activity,"
Once the attackers obtained credentials through RustyStealer, they exploited this access to infiltrate networks and facilitate the deployment of Ymir ransomware. The report detailed how attackers utilized WinRM and PowerShell to penetrate security measures, deploying SystemBC malware to create covert communication channels.
"We have seen initial access brokers invade an organization and ensure persistence. Ymir was deployed to the targeted system shortly after," notes Kaspersky. This emphasis on persistence highlights the attackers' strategic focus on maintaining long-term access and control within compromised environments.

Beyond the immediate threat of the ransomware itself, the Kaspersky analysis emphasizes a critical concern regarding organizational responses to cyber incidents. "Alerts were triggered two days prior to the ransomware incident, and the lack of action on the critical system warnings allowed the attackers to launch the ransomware," the report concludes, suggesting that more robust and proactive security strategies are essential.
"Alerts were triggered two days prior to the ransomware incident, and the lack of action on the critical system warnings allowed the attackers to launch the ransomware,"
The current threat landscape emphasizes the need for organizations to improve their response mechanisms, moving beyond reliance solely on endpoint protection solutions. Kaspersky's report also includes specific Indicators of Compromise (IoCs) for organizations to watch for, underscoring the necessity for vigilance in today’s cyber environment.
As cybersecurity threats continue to evolve in sophistication and coordination, Ymir ransomware serves as a stark reminder of the importance of comprehensive threat management strategies. The development of this new ransomware variant is indicative of the larger trends facing businesses and organizations, making it crucial to stay informed and prepared for emerging cyber threats.